G Network Configuration for Digital Forensics
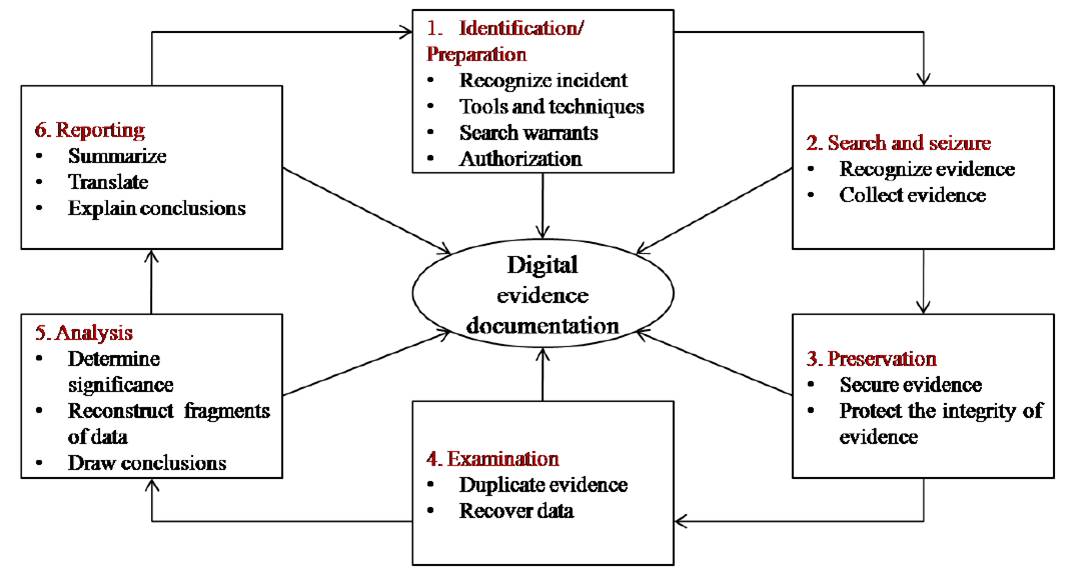
Digital forensics is the application of science to the identification, collection, examination, and analysis of data while preserving the integrity of the information and maintaining a strict chain of custody for the data. A thorough G Network Configuration for Digital Forensics is essential for conducting digital investigations and gathering evidence in a secure and reliable manner.
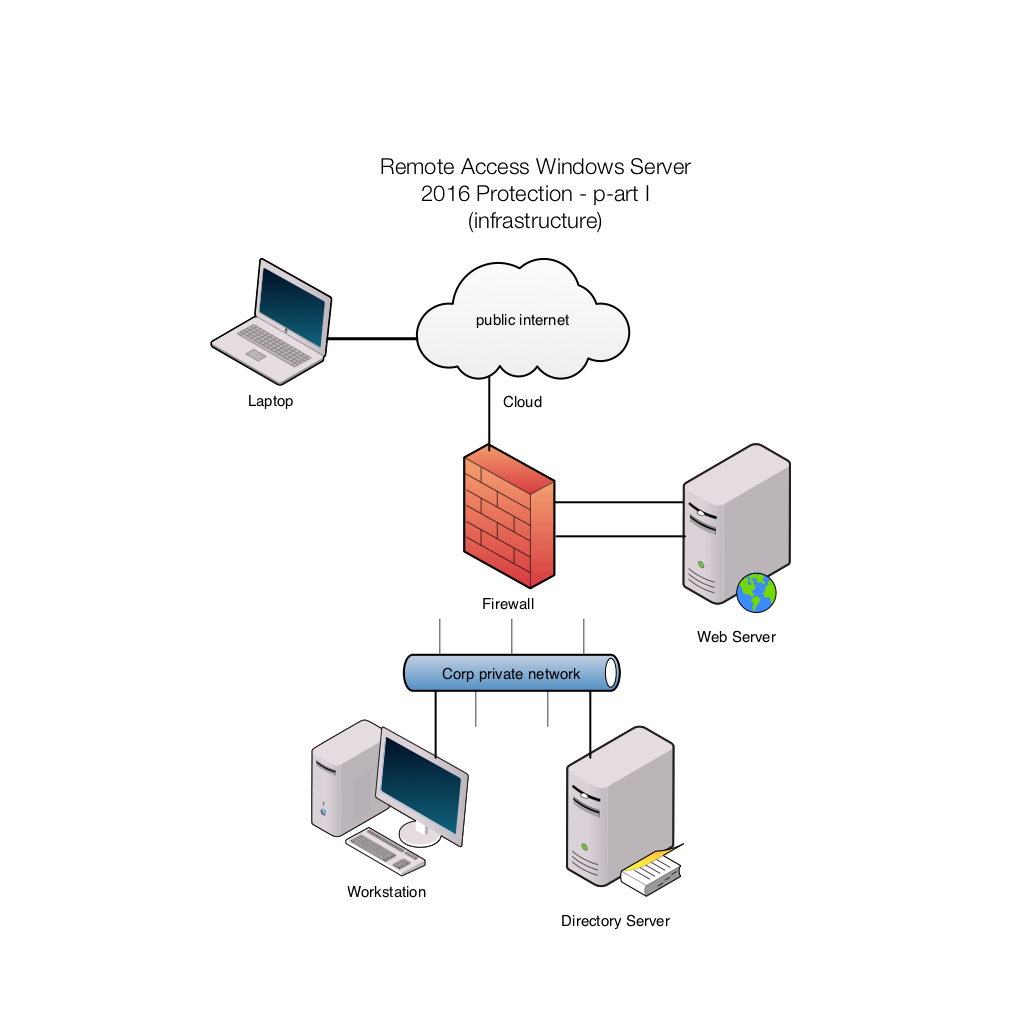
Physical Configuration and Network Topology
Physical configuration and network topology are less volatile and have a longer lifespan than other logs. Archival media, such as DVD-ROM, CD-ROM, or tape, contain the least volatile data because the digital information does not change automatically unless damaged. Device manufacturers and their customers can use G Network Configuration for Digital Forensics to establish a baseline of standard features to include in the architecture of network devices and appliances.
Network Configuration for Digital Forensics
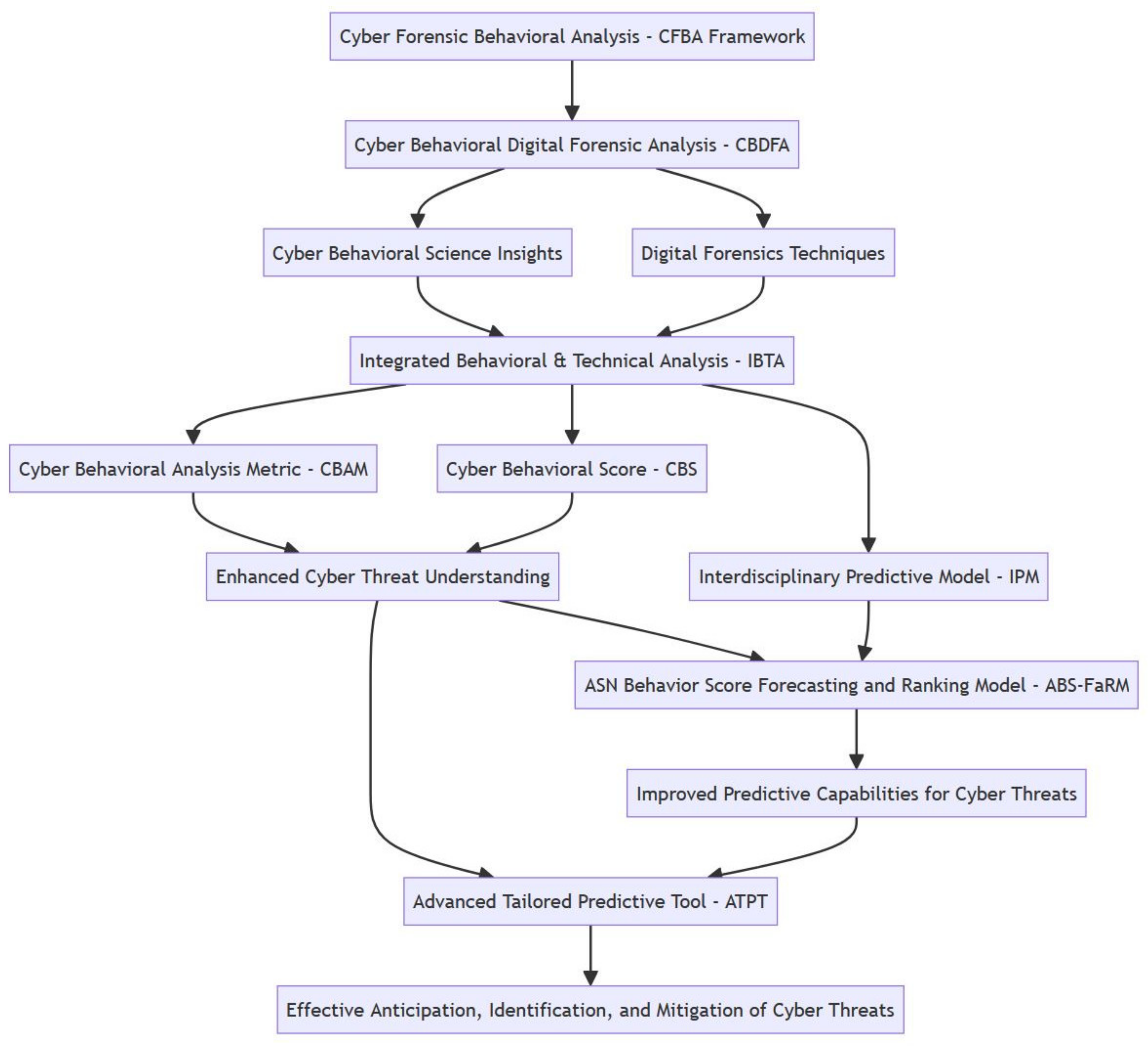
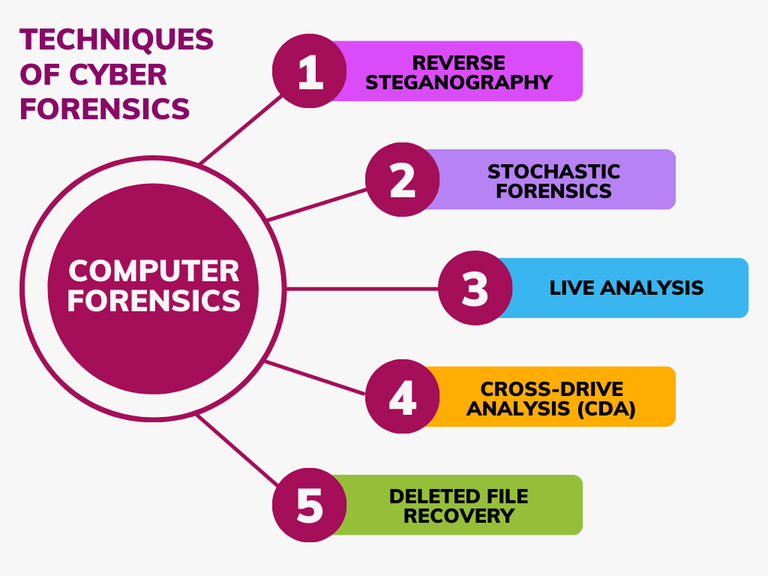
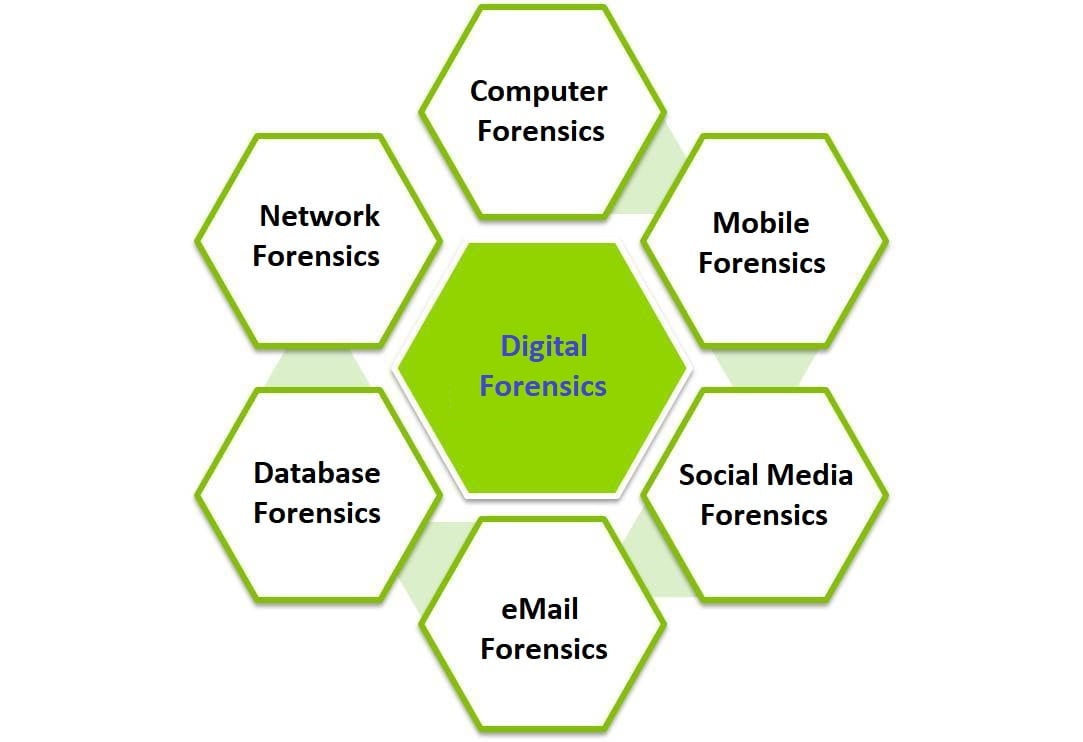
As we can see from the illustration, G Network Configuration For Digital Forensics has many fascinating aspects to explore.
- Imperva recommends setting up a virtual digital forensics lab with a stable and controlled environment to facilitate digital investigations.
- Configure the network for segregation of duties, controlling user access to network resources, and implementing a least privilege model.
- Ensure that all devices and systems are properly configured and certified, and continuously monitored for security updates and compliance with security policies.
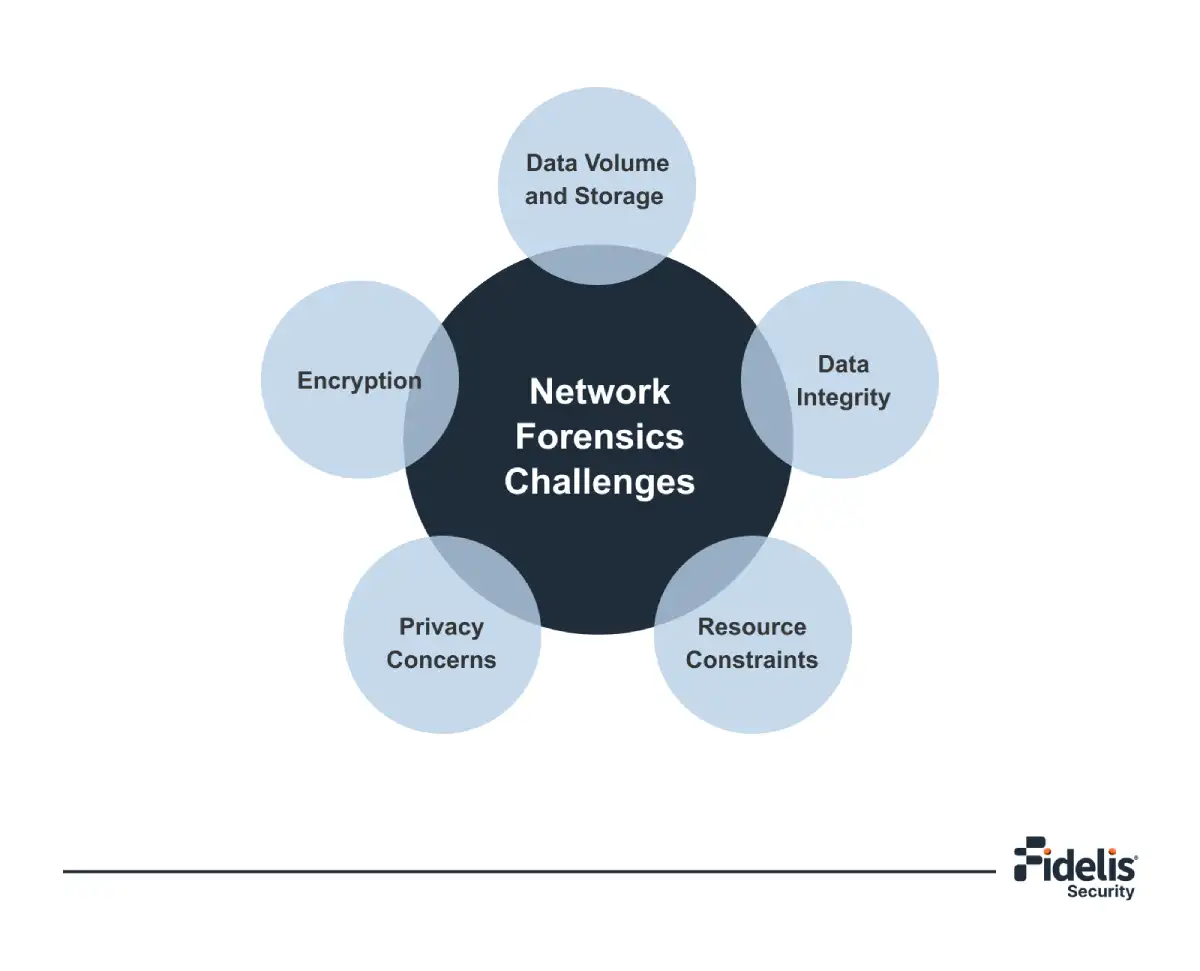
- Implement a robust logging and monitoring system to detect and alert on suspicious activity, facilitating faster incident response.
- Use digital forensics tools and capabilities to investigate digital evidence and respond to security incidents efficiently.
- Regularly test and update your network configuration to ensure it remains compliant with regulatory requirements and industry standards.
- Defining clear policies and procedures for implementing and maintaining network security.
- Implementing access controls, authentication, and authorization mechanisms.
- Monitoring network traffic and log analysis to detect and respond to security incidents.
- Storing and preserving forensic evidence in a tamper-proof and easily accessible manner.
- Collaborating with digital forensics experts to develop a solid incident response strategy.
Moving forward, it's essential to keep these visual contexts in mind when discussing G Network Configuration For Digital Forensics.
Conclusion
The G Network Configuration for Digital Forensics is a vital component of conducting digital investigations effectively. By following the best practices outlined above, you can ensure that your network configuration is secure, reliable, and efficient for digital forensics. Regular updates to your network configuration will help you meet evolving security threats and maintain a proactive approach to security.