Computer Security Best Practices: Protecting Your Digital Assets
In today's digital age, computer security has become a top priority for individuals and organizations alike. With the increasing number of cyber threats and data breaches, it's essential to implement robust security measures to protect your digital assets. In this article, we'll discuss the top computer security best practices to help you safeguard your data and prevent cyber attacks. Computer security best practices are guidelines and protocols that help individuals and organizations protect their digital assets from cyber threats. By following these best practices, you can reduce the risk of cyber attacks, prevent data breaches, and maintain the confidentiality, integrity, and availability of your data.1. Keep Your Software Up-to-Date
One of the most critical computer security best practices is to keep your software, including your operating system, browser, and other applications, up-to-date. This ensures that you have the latest security patches and updates, which can help prevent exploitation of known vulnerabilities.2. Use Strong and Unique Passwords
Using strong and unique passwords is another essential computer security best practice. Avoid using easily guessable passwords, such as your name, birthdate, or common words. Instead, use a combination of uppercase and lowercase letters, numbers, and special characters. Consider using a password manager to generate and store complex passwords.3. Enable Two-Factor Authentication (2FA)
Two-factor authentication (2FA) adds an extra layer of security to your accounts by requiring a second form of verification, such as a code sent to your phone or a biometric scan, in addition to your password. Enable 2FA on all your accounts, especially for sensitive information like email, bank accounts, and social media.4. Use Encryption to Protect Data

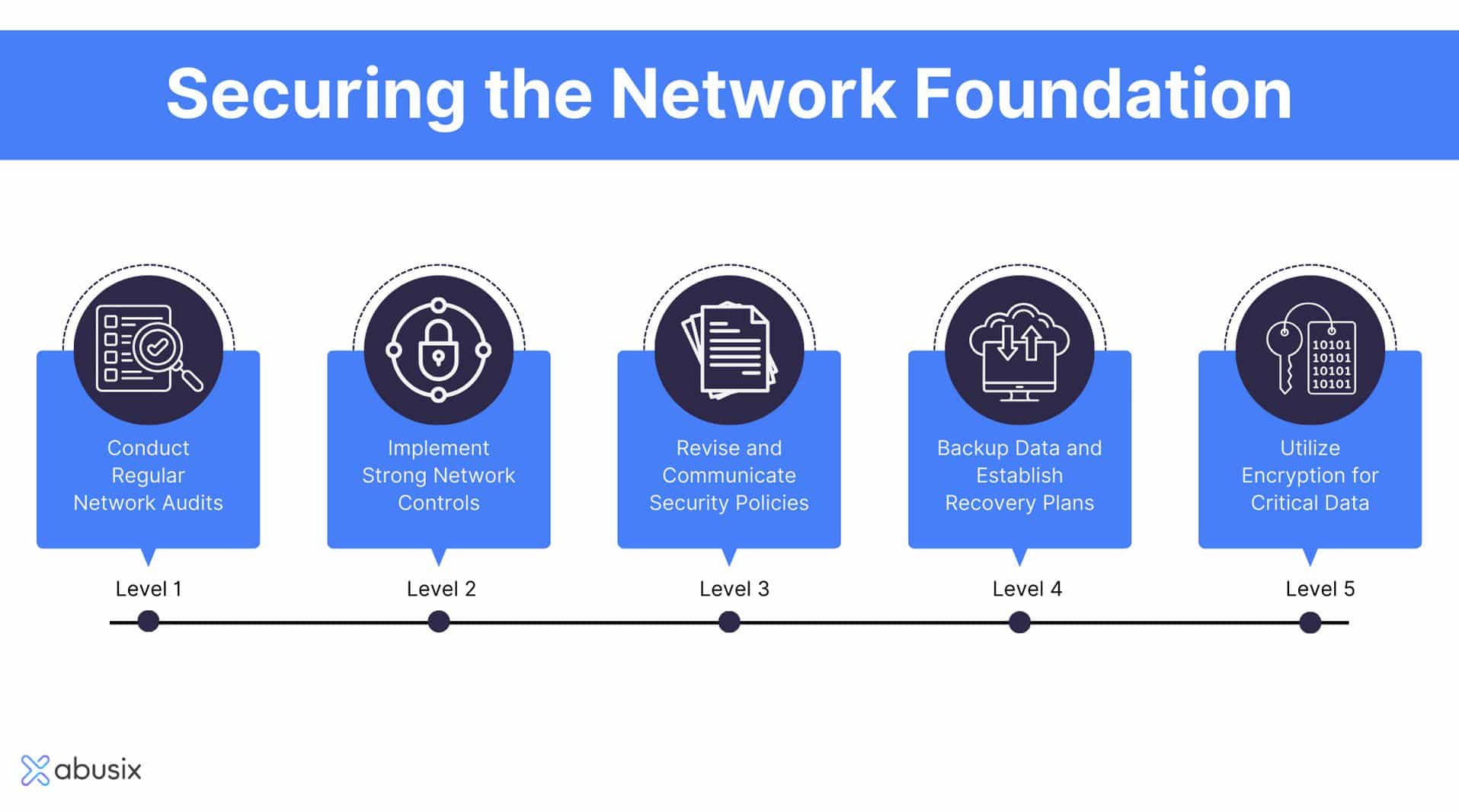
Moving forward, it's essential to keep these visual contexts in mind when discussing Computer Security Best Practices.
Encryption is a powerful computer security best practice that protects your data from unauthorized access. Use encryption to secure your sensitive data, such as financial information, personal identifiable information (PII), and confidential business data.5. Install Anti-Virus and Anti-Malware Software
Anti-virus and anti-malware software can help detect and prevent malware from infecting your device. Install reputable security software and keep it updated to ensure you have the latest virus definitions.6. Use a Firewall
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. Enable the firewall on your device and network to prevent unauthorized access to your system.7. Use Secure Communication Protocols
Secure communication protocols, such as HTTPS, ensure that data transmitted between your device and a server is encrypted and secure. Use secure protocols for online transactions, email, and other sensitive activities.8. Regularly Back Up Your Data

Such details provide a deeper understanding and appreciation for Computer Security Best Practices.
Regular backups are essential to ensure that your data is safe in case of a disaster or cyber attack. Use an external hard drive or cloud storage to back up your critical data regularly.



.png)