Best Practices for Encrypted Data Storage
Classify Your Data
The first step in implementing effective encryption is to classify your data based on its sensitivity and confidentiality. This involves categorizing your data into different levels of protection, such as public, internal, confidential, or highly confidential. For example, your organization might decide that highly confidential data should use asymmetric encryption, while public data doesn't require encryption.
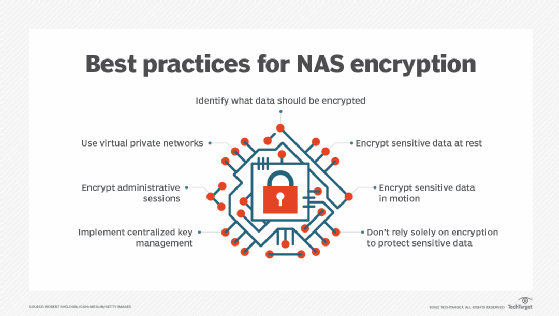
Create an Encryption Strategy
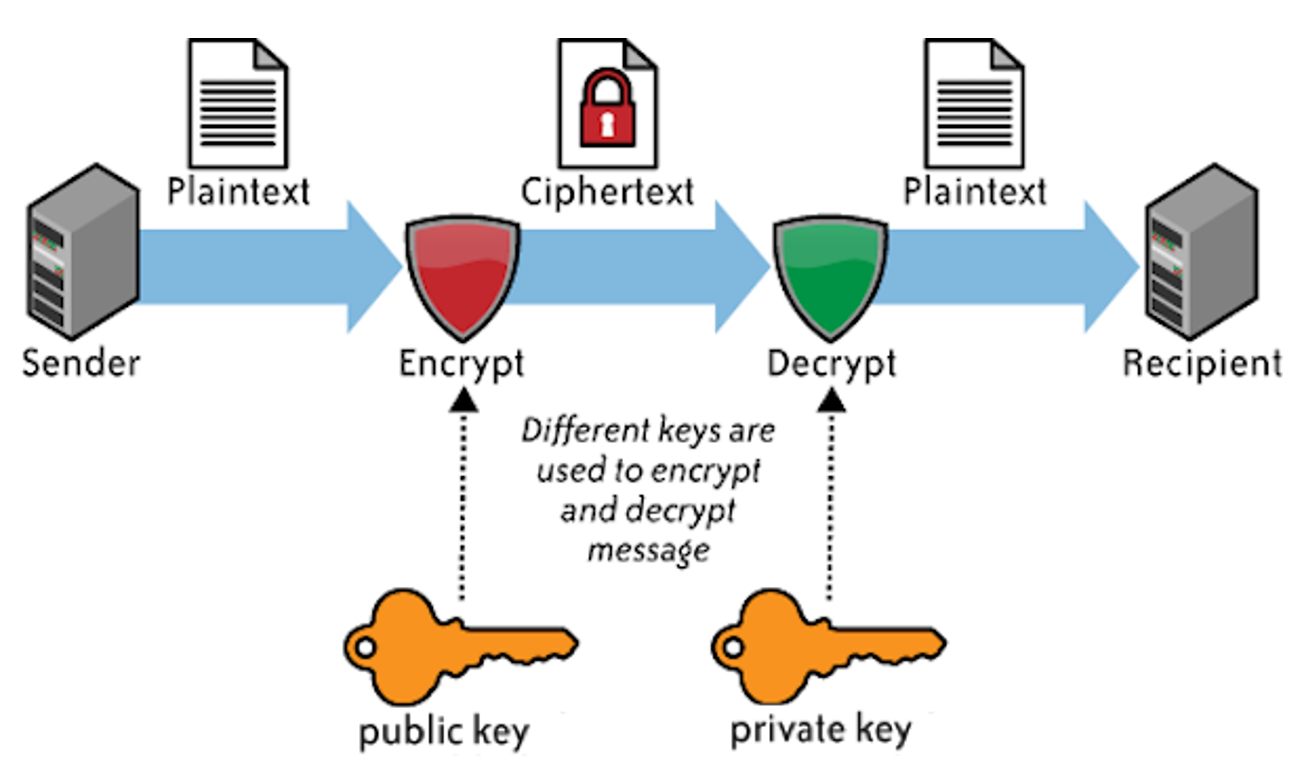
Once you've classified your data, you can create an encryption strategy for your organization based on the level of protection required for each category. This strategy should include the type of encryption to be used, such as symmetric or asymmetric encryption, and the key management process. For instance, you might decide to use symmetric encryption for public data and asymmetric encryption for confidential data.
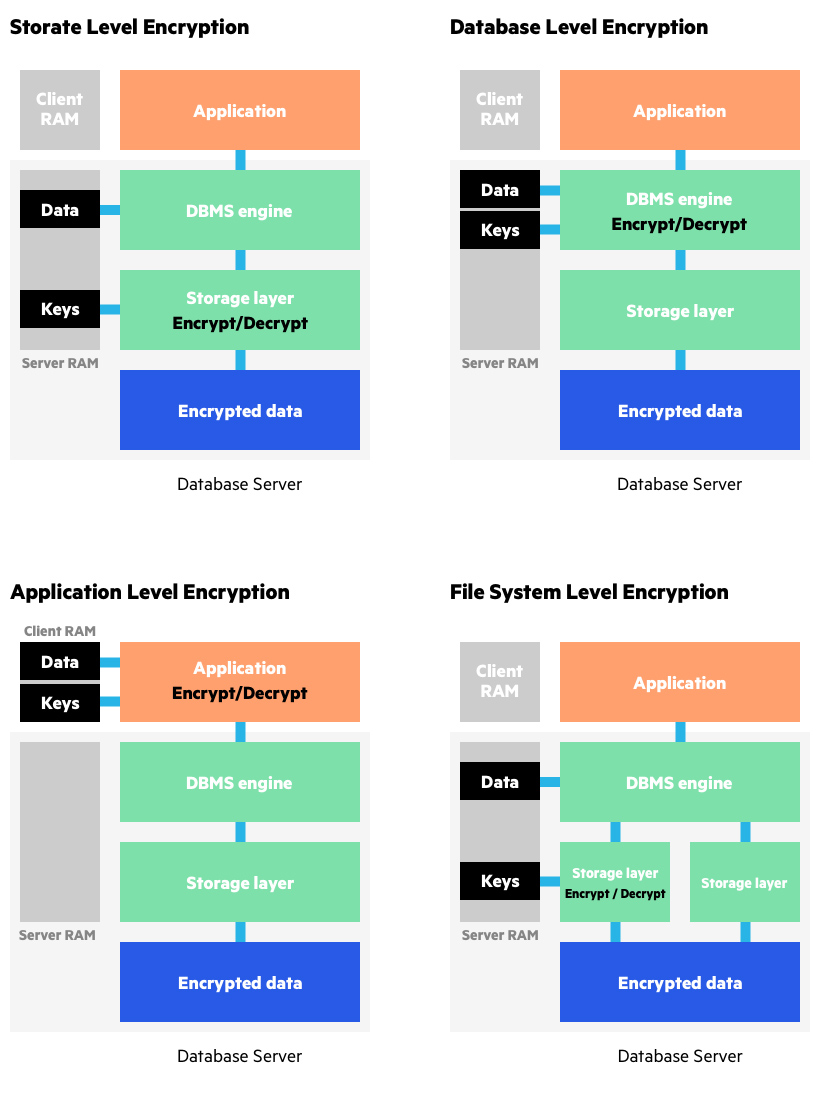
Select Appropriate Encryption Methods

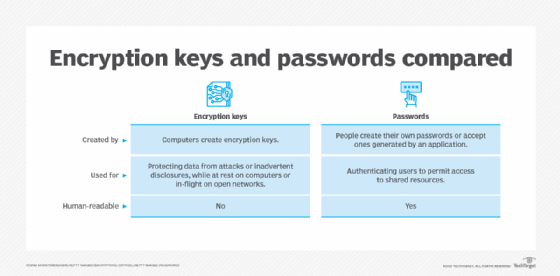
There are various encryption methods available, including symmetric, asymmetric, and hash-based encryption. Symmetric encryption uses the same key for both encryption and decryption, while asymmetric encryption uses a pair of keys, one for encryption and another for decryption. Hash-based encryption uses a one-way hash function to ensure data integrity. Choose the method that best suits your organization's needs and data sensitivity level.
Implement Strong Key Management Strategies
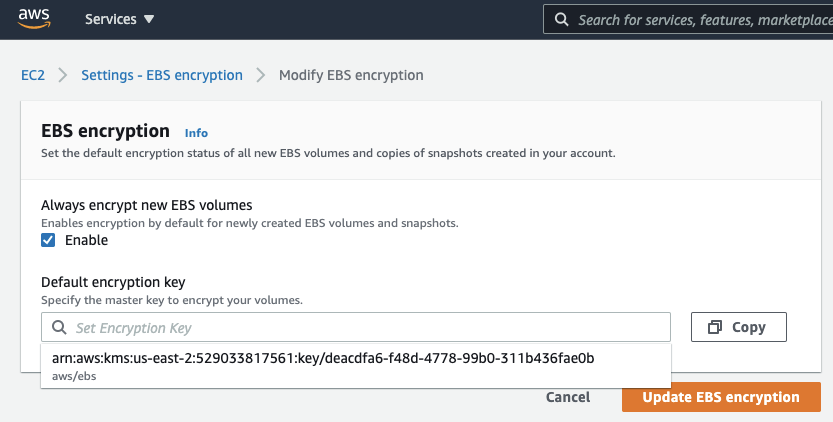
A strong key management strategy is crucial for ensuring the security of your encrypted data. This includes generating and storing keys securely, rotating keys regularly, and implementing access controls to prevent unauthorized access to keys. Use a secure key management system to store and manage your encryption keys.
Maintain Up-to-Date Systems
Regularly update your encryption software and systems to ensure you have the latest security patches and features. This will help protect your organization from known vulnerabilities and emerging threats. Additionally, ensure that your systems and software are properly configured to support encryption.
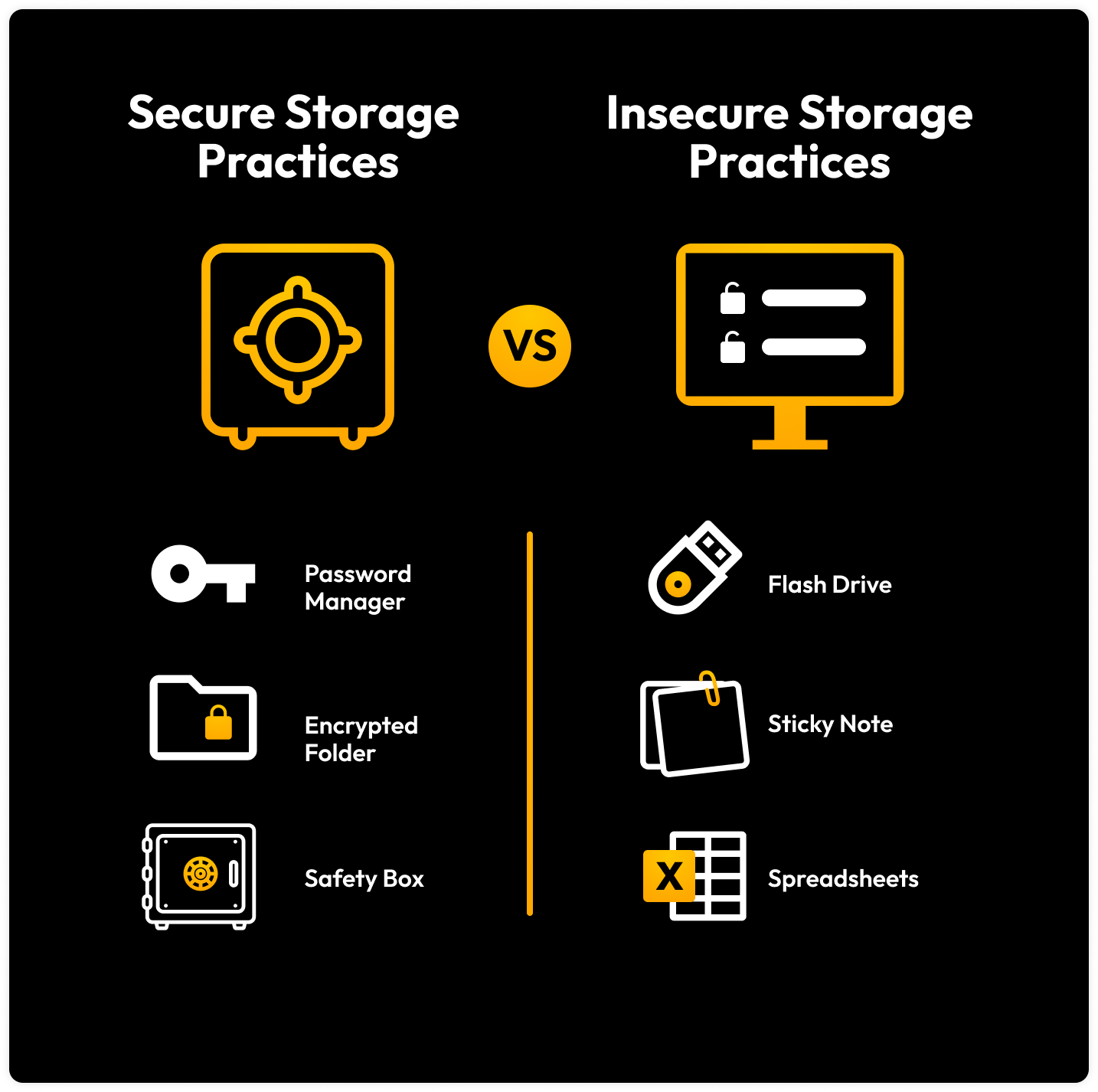
Store Encrypted Data Securely
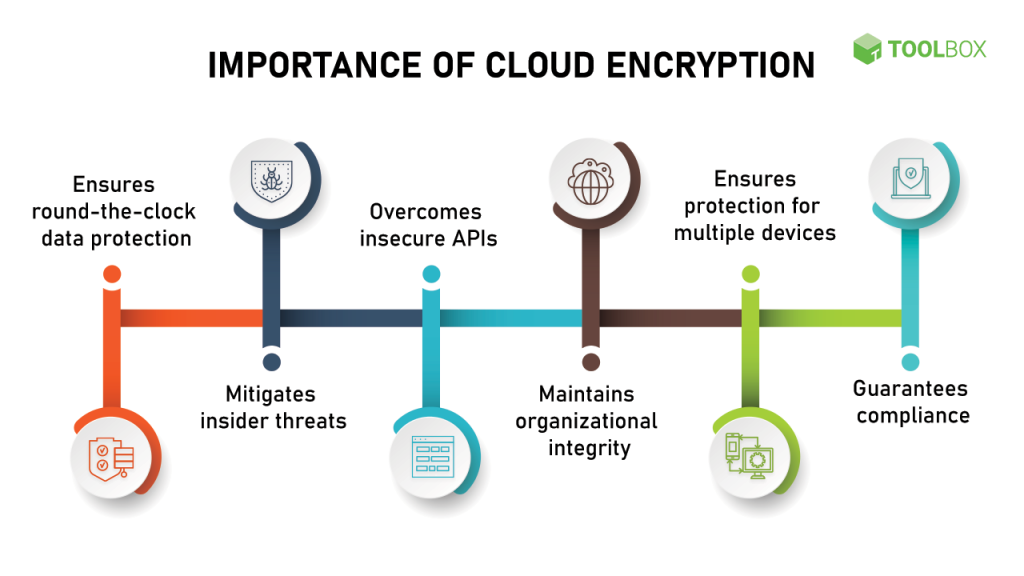
When storing encrypted data, ensure that it's stored securely and separately from the original data. Use secure storage solutions, such as encrypted cloud storage or on-premises storage systems, to protect your data from unauthorized access. Regularly back up your encrypted data to prevent data loss in case of a disaster or system failure.
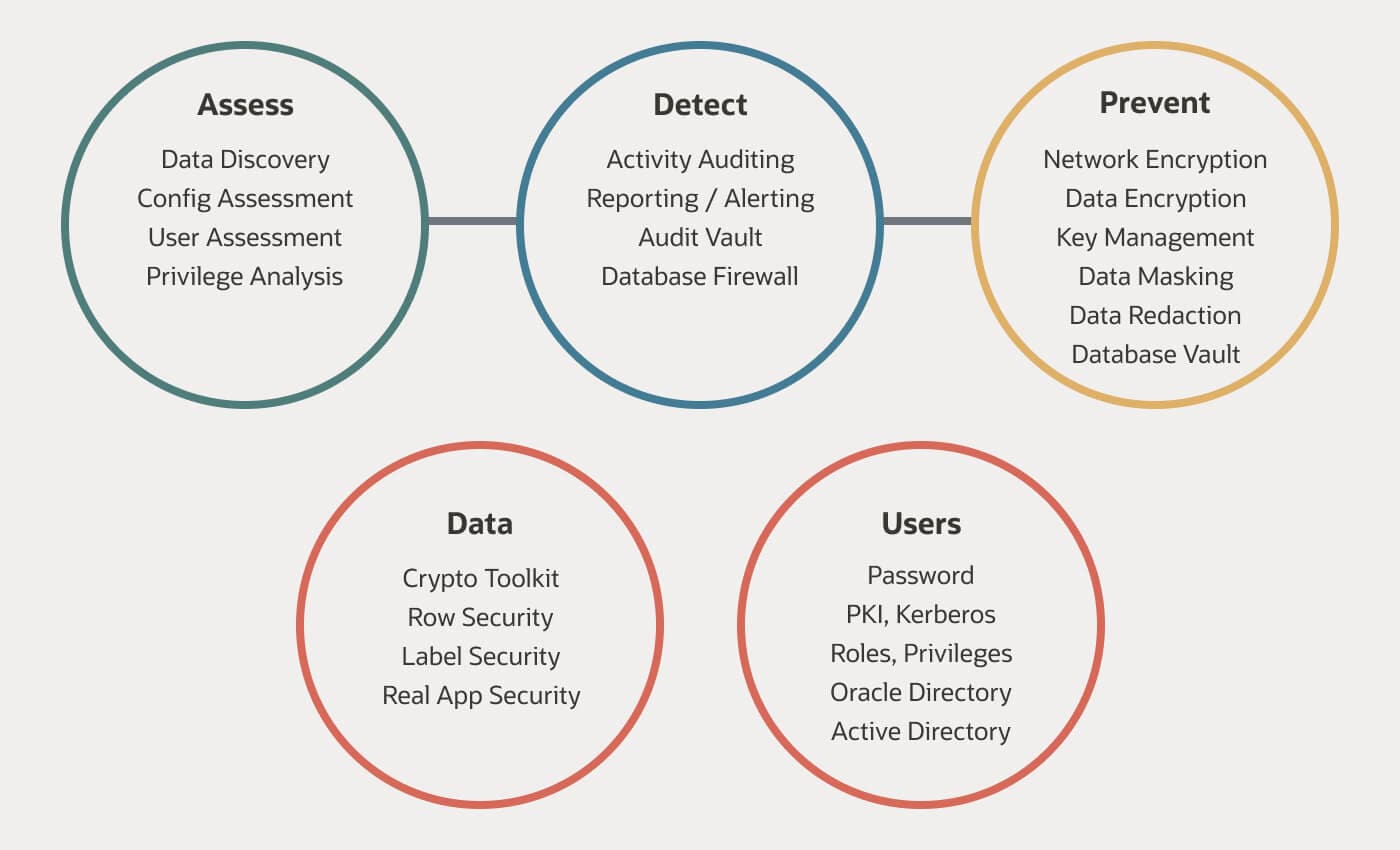
Monitor and Manage Your Data
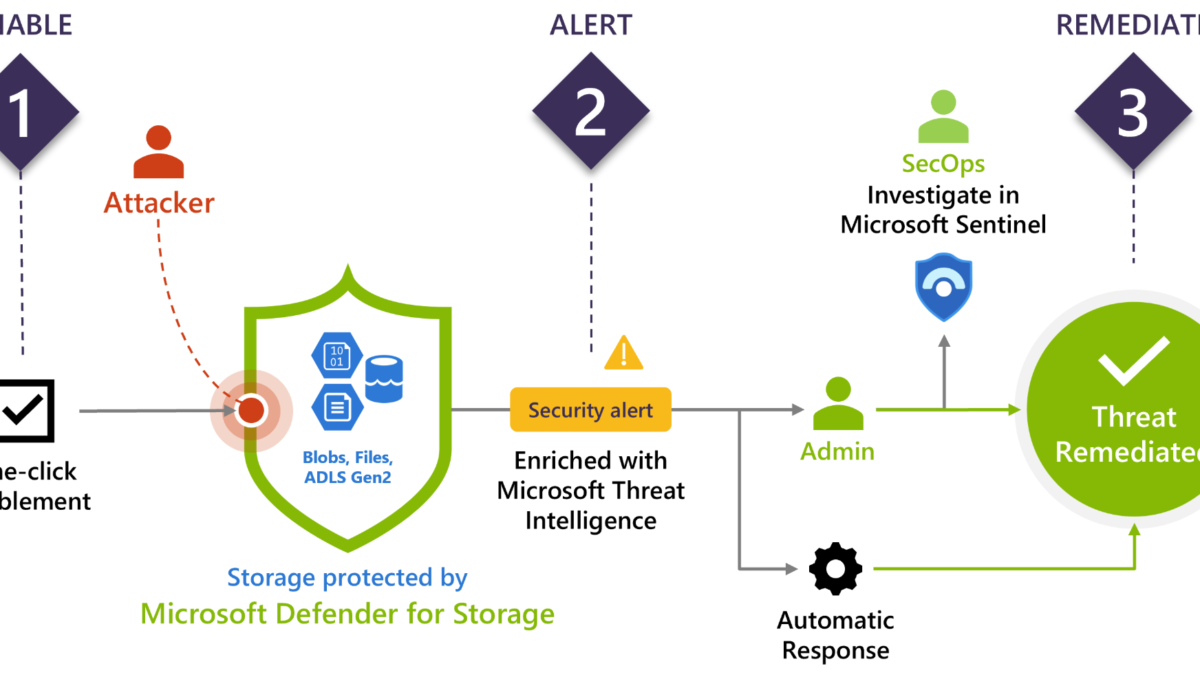
Regularly monitor and manage your encrypted data to ensure it remains secure and compliant with regulatory requirements. This includes checking for data breaches, reviewing access controls, and updating your encryption strategy as needed. Use monitoring tools to detect potential security threats and address them promptly.
Best Practices for Encrypted Data Storage
- Use Full Disk Encryption: Encrypting the entire disk where your sensitive data is stored provides an additional layer of security.
- Implement Strong Access Controls: Use complex passwords, enable two-factor authentication, and regularly review user permissions to ensure that only authorized personnel have access to sensitive data.
- Use Secure Storage Solutions: Store encrypted data securely and separately from the original data using secure storage solutions.
- Maintain Up-to-Date Systems: Regularly update your encryption software and systems to ensure you have the latest security patches and features.
- Monitor and Manage Your Data: Regularly monitor and manage your encrypted data to ensure it remains secure and compliant with regulatory requirements.