How to Stop Phishing Attacks: A Comprehensive Guide
Phishing attacks are currently the most common and effective type of cyber attack, with hackers using increasingly sophisticated tactics to trick victims into revealing sensitive information. In this guide, we'll explain what phishing is, provide tips on how to defend against these attacks, and share valuable resources from our partners to help you stay safe online.
What is Phishing?
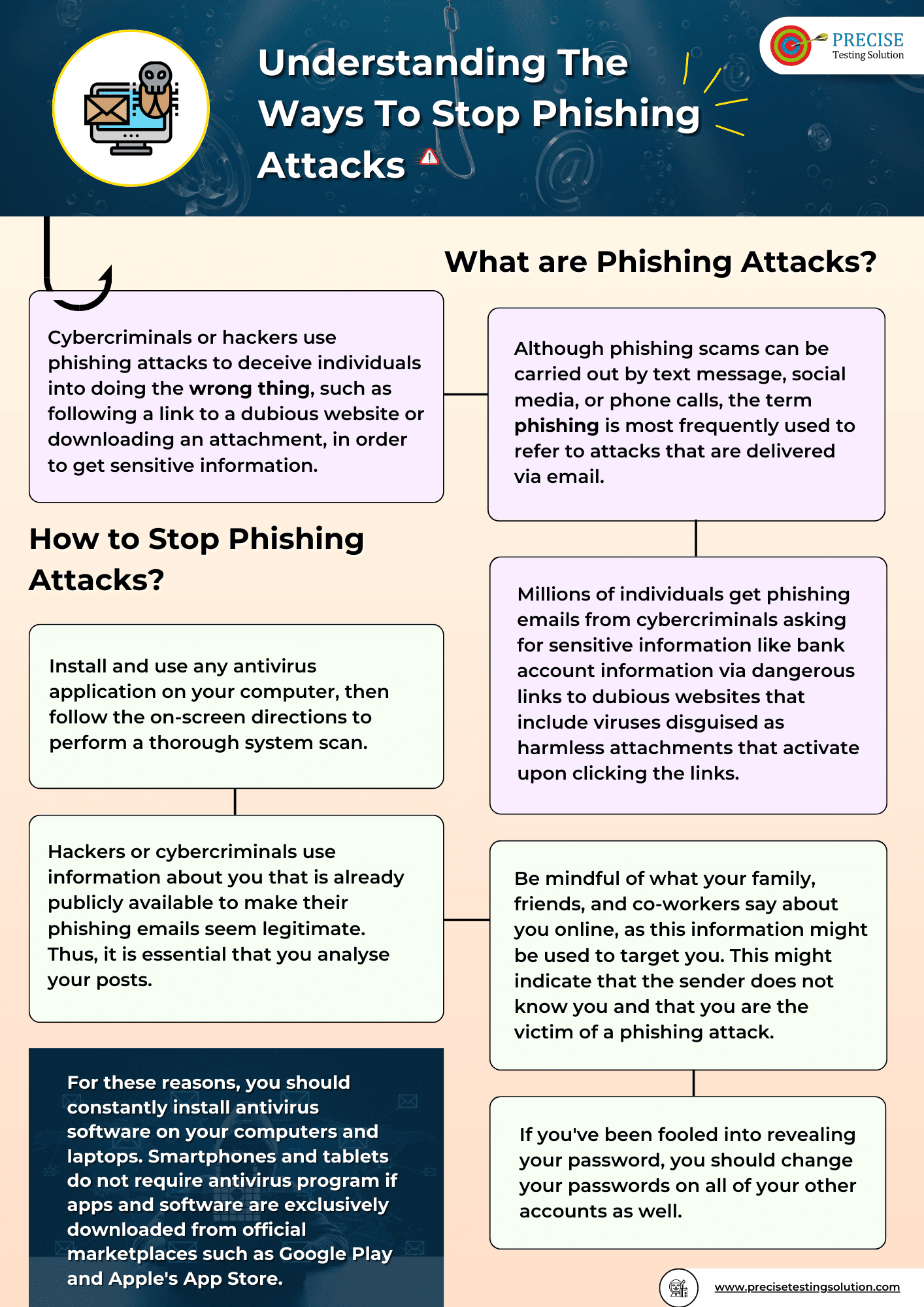
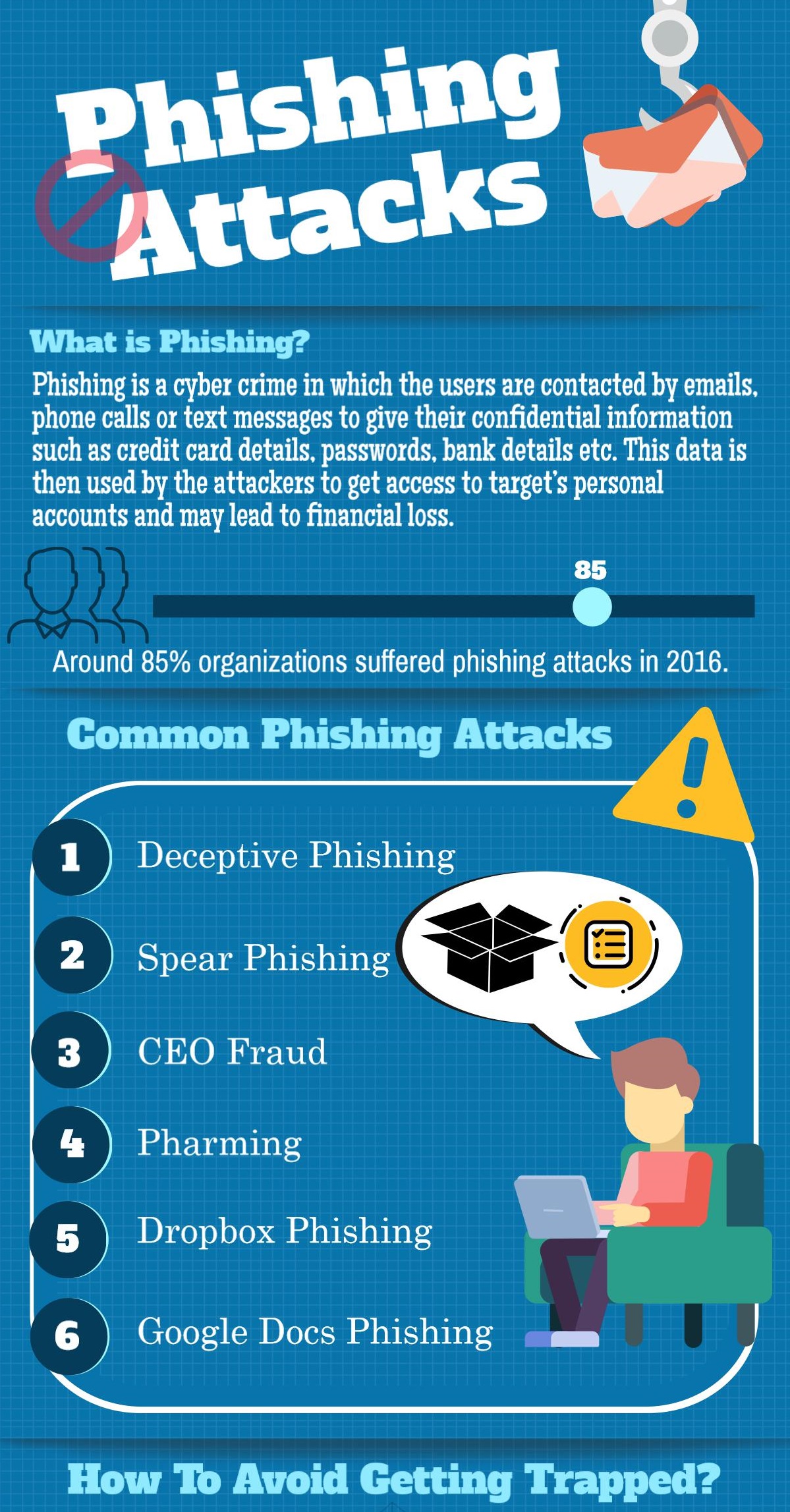
Phishing is a type of social engineering attack where attackers send fake emails or messages that appear to be from a legitimate source, aiming to trick victims into revealing sensitive information such as passwords, credit card numbers, or Social Security numbers. These attacks are often successful because they appear to be authentic and can evade even the most alert users.
How to Identify Phishing Attacks
To defend against phishing attacks, it's essential to know how to spot these attacks. Here are some common tactics used by cybercriminals:

- Urgency-based attacks: These attacks create a sense of urgency, asking you to act quickly to resolve an issue or take advantage of a limited-time offer.
- Personalized attacks: These attacks use information gathered from your social media profiles, email communications, or online search history to make the attack more convincing. li> Updates or service notifications: These attacks claim that your account or software needs to be updated or that a service notification requires your login credentials.
- Transparent grafic-based attacks: These attacks use fake emails or messages with overtly designed graphics to distract you from the real intent of the message.
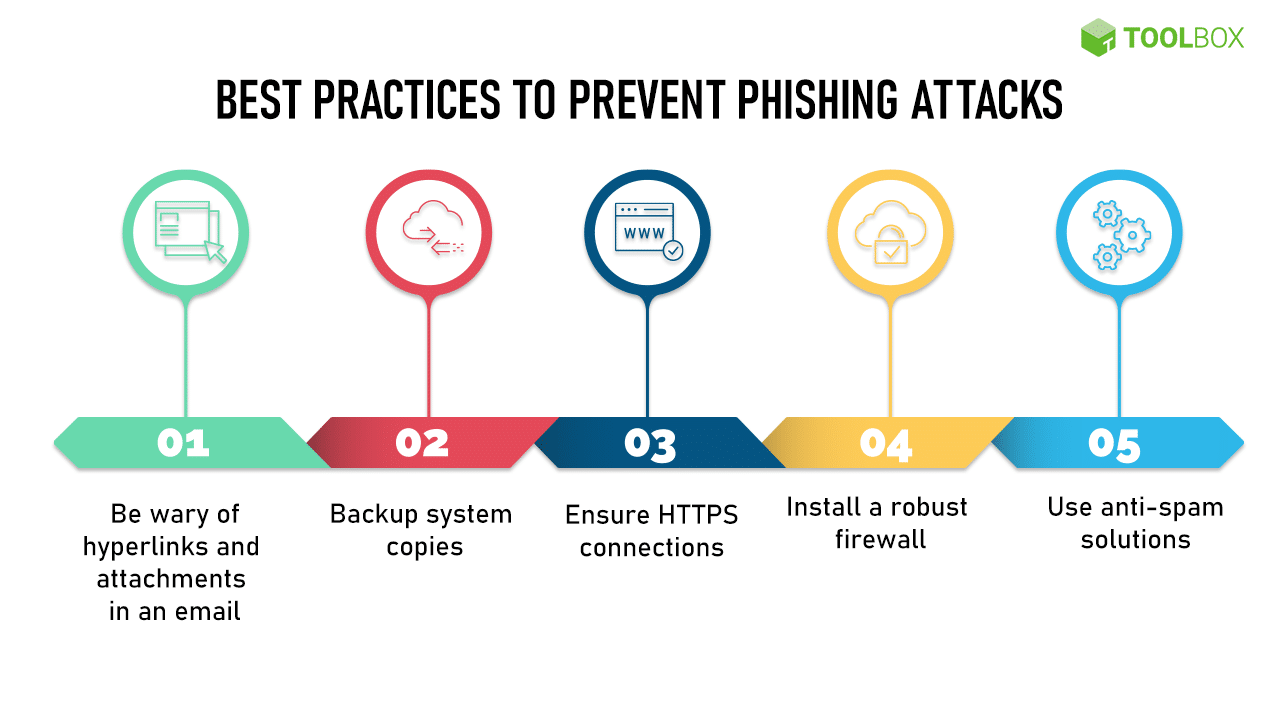
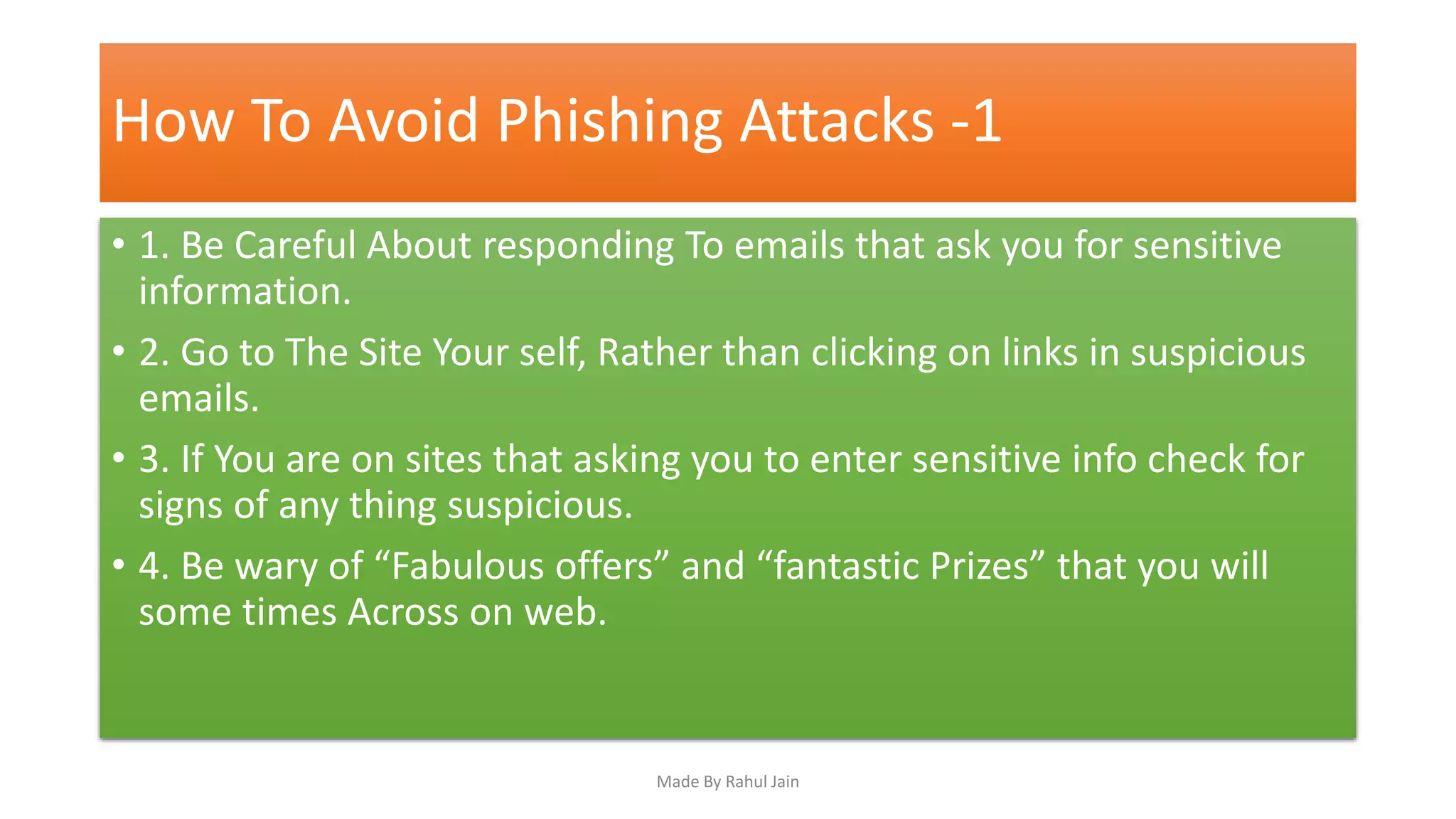
While awareness is crucial, stopping phishing attacks requires more than just being vigilant. Here are some key steps you can take:
- Practice cybersecurity awareness: Educate yourself and your employees on the signs of phishing attacks, how to identify and report them, and what to do if you receive a suspicious message.
- Implement multi-factor authentication: This adds an extra layer of security to your accounts and makes it harder for attackers to gain access.
- Use a trusted password manager: This helps you generate strong, unique passwords and saves you time storing and filling in credentials.
- Keep software up-to-date: This ensures you have the latest security patches and updates for your operating system, browser, and applications.
- Use a reputable security solution: This provides an additional layer of protection against malware and phishing attacks, including AI-powered defenses that can detect and block new threats.
Effective Phishing Prevention in 2026
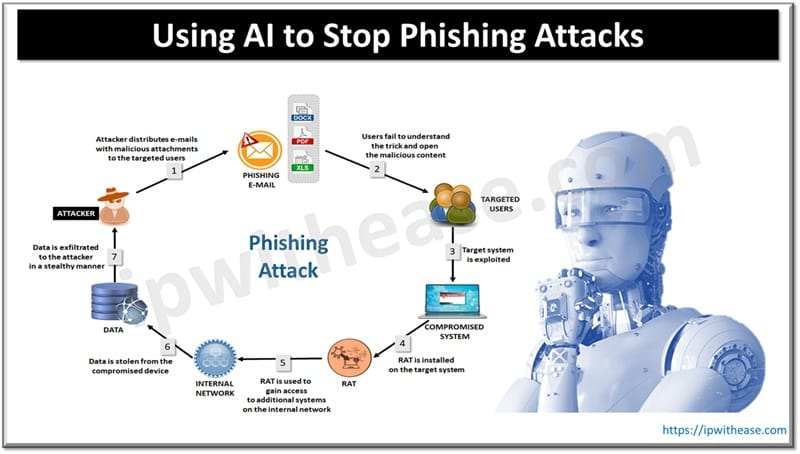
As AI-powered phishing attacks escalate, it's essential to stay ahead of these threats. Here are some essential strategies for organizations to detect and prevent phishing attacks effectively:

- Deploy AI-powered endpoint security solutions: These solutions can analyze traffic and detect anomalies to prevent phishing attacks and other types of threats.
- Implement a targeted phishing simulation: This process simulates real-world phishing attacks to test users' knowledge and raise awareness about the risks.
- Enhance employee training: This should include ongoing education on phishing awareness, social engineering tactics, and incident response procedures.
- Monitor and analyze network traffic: This helps identify and block potential threats before they reach users.
Protect Yourself from Phishing
By understanding how to identify and prevent phishing attacks, you can significantly reduce the risk of cyber threats. Here are some key actions to take:
- Verify sender authenticity: Be cautious when receiving emails or messages from unknown or unfamiliar sources, especially if they ask for sensitive information.
- Be wary of urgency-based attacks: If an attack creates a sense of urgency, beware that it might be an attempt to get you to act without thinking.
- Regularly review online accounts: Check your statements, transactions, and payment history to ensure everything is in order.
Conclusion
Phishing attacks can have severe consequences, including financial loss, reputational damage, and compromised sensitive information. By following these guidelines on how to stop phishing attacks, you'll be better equipped to identify, prevent, and respond to these types of cyber threats. Stay vigilant, stay informed, and protect yourself and your organization with effective cybersecurity practices.





.png)