G Network Security Setup for BYOD (Bring Your Own Device)
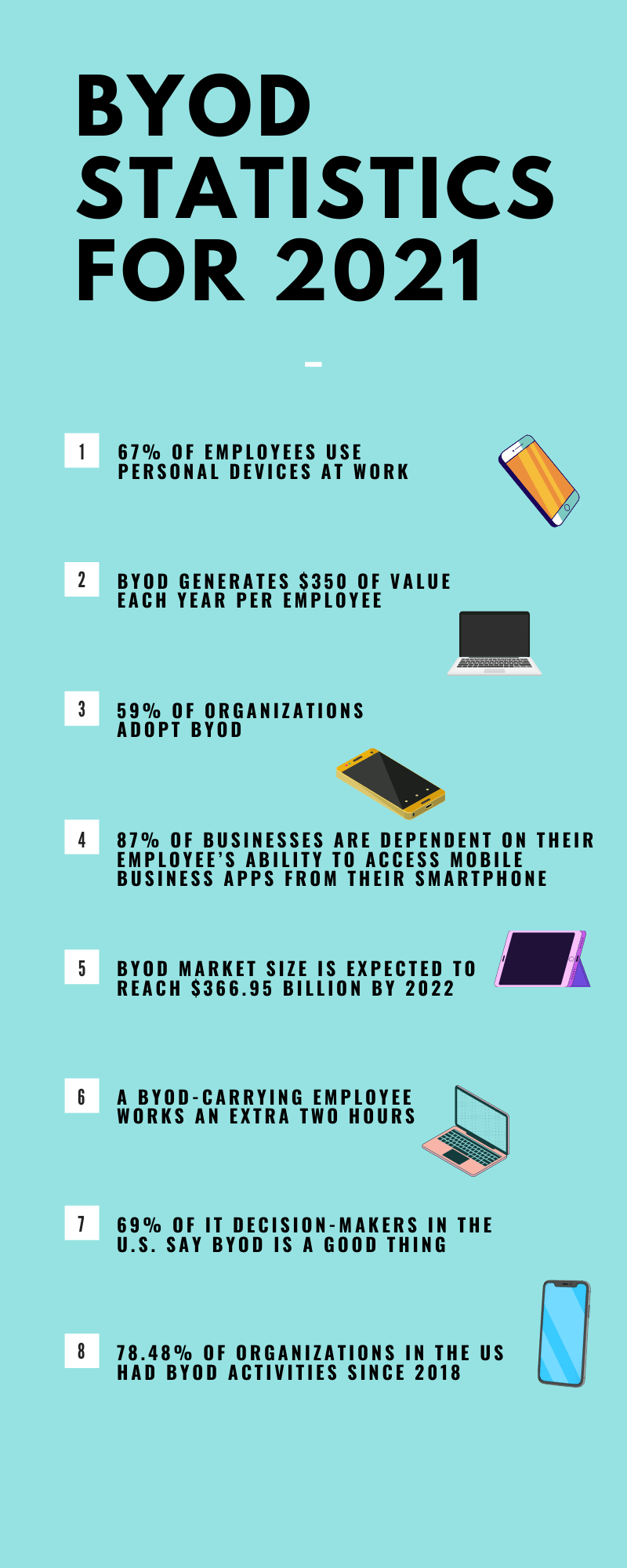
In today's digital age, the Bring Your Own Device (BYOD) policy has become a popular approach in the workplace. BYOD allows employees to use their personal devices for work-related activities, which can improve productivity and job satisfaction. However, this approach also raises significant security concerns, especially when it comes to protecting sensitive business data.
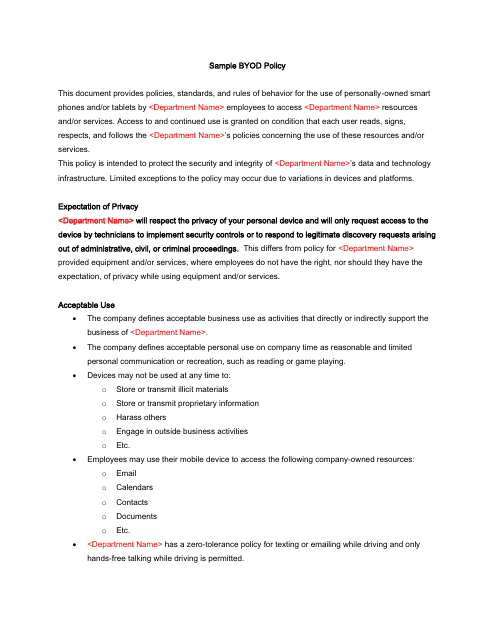
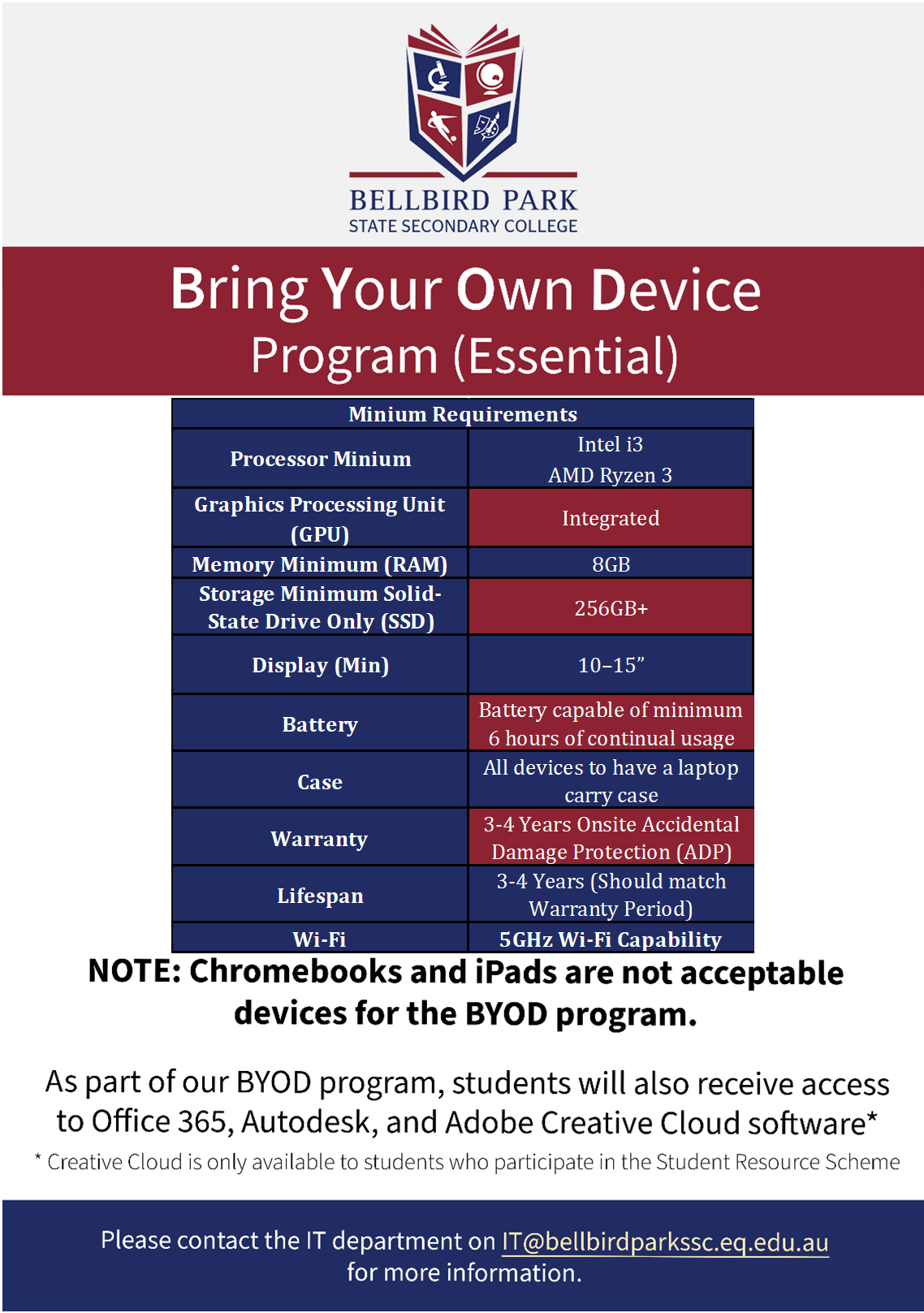
BYOD refers to the practice of using personal devices for work-related activities, such as laptops, smartphones, or tablets. This approach has been adopted by many companies to improve employee flexibility and productivity. However, it also brings new security challenges that IT administrators must address to protect business data.
The Risks of BYOD
There are several risks associated with BYOD, including:

Implementing G Network Security Setup for BYOD
To address these security concerns, IT administrators can implement the following measures:
- Implement a robust mobile device management (MDM) solution to manage and control devices
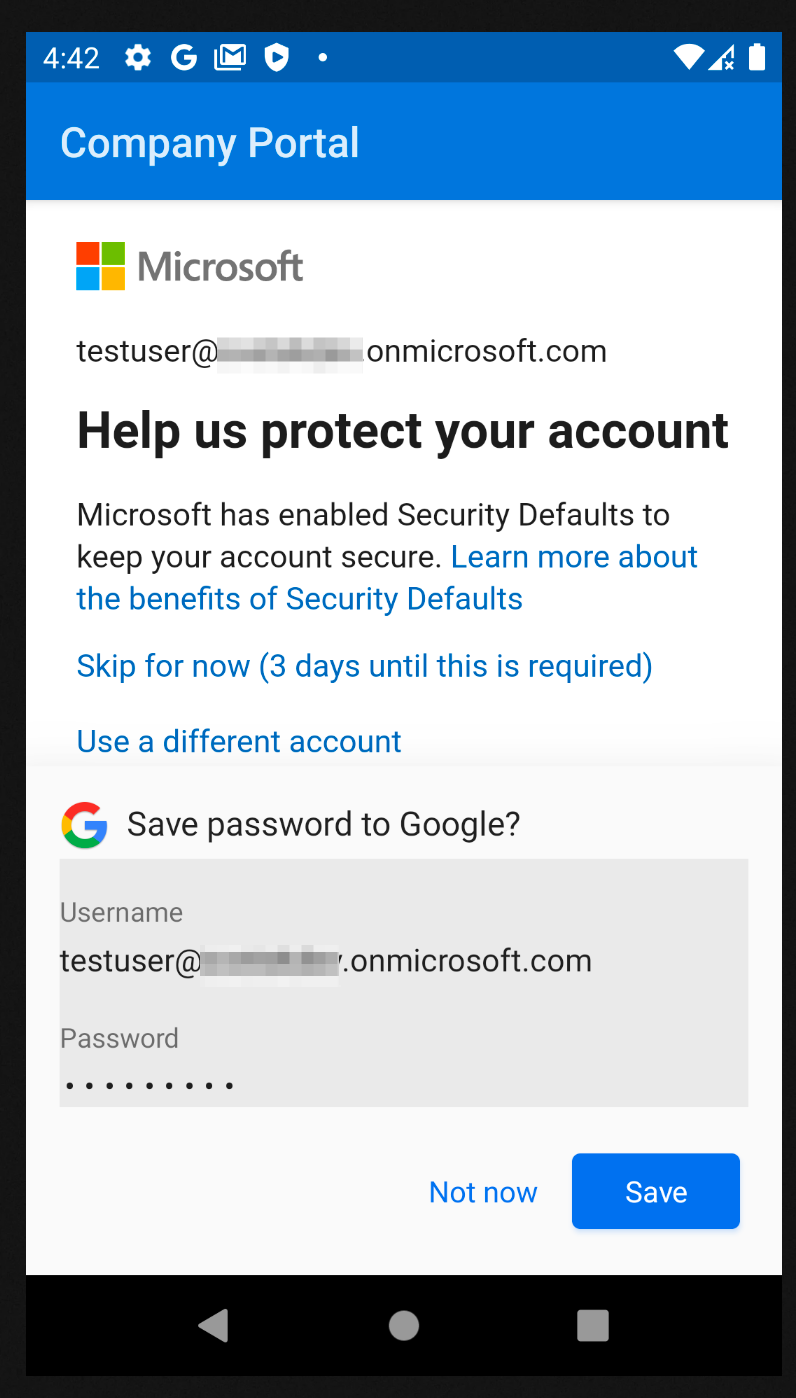
- Enforce strong passwords and multi-factor authentication (MFA)
- Encrypt sensitive data and device communications
- Regularly update and patch devices with the latest security patches
- Monitor device activity and detect potential security threats
Best Practices for BYOD Security

Best practices for BYOD security include:
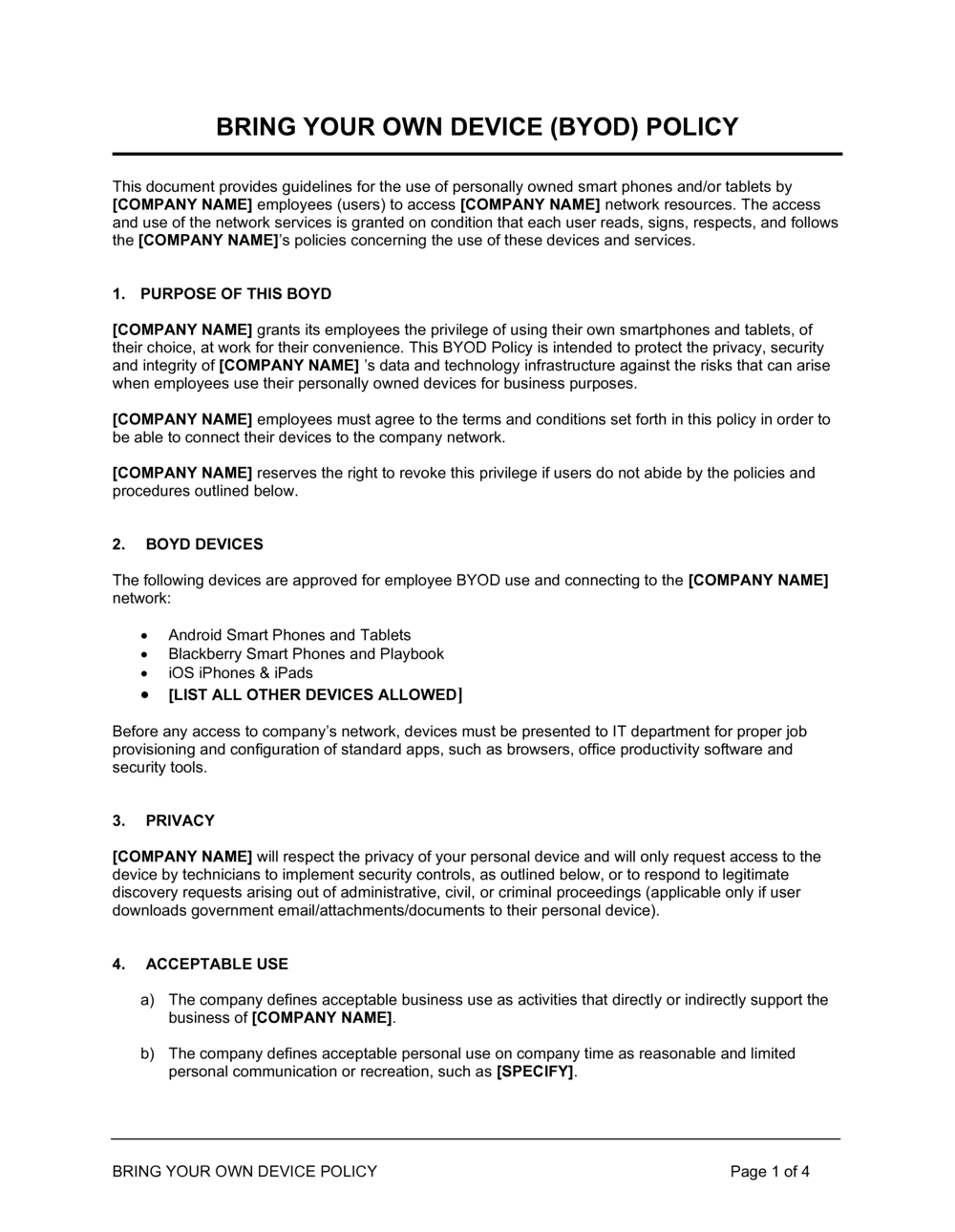
- Clearly define BYOD policies and guidelines
- Establish protocols for device enrollment and approval
- Implement device-level security measures, such as encryption and MFA
- Regularly monitor device activity and address security concerns
- Provide employee education and training on BYOD security best practices
Benefits of BYOD Security
Implementing a secure BYOD policy can provide several benefits, including:

Moving forward, it's essential to keep these visual contexts in mind when discussing G Network Security Setup For Byod (Bring Your Own Device).
- Improved productivity and employee satisfaction
- Cost-effective, as employees use their personal devices
- Increased flexibility and convenience for employees
- Reduced IT costs and support overhead
Conclusion
BYOD has become a popular approach in the workplace, offering numerous benefits. However, it also brings significant security concerns that must be addressed. Implementing a secure G Network Security Setup for BYOD can help organizations protect sensitive data and mitigate security risks. By following best practices and guidelines, organizations can ensure a secure and productive BYOD environment.